Businesses have historically used IT asset management (ITAM) to keep tabs on their software and hardware assets, which might have been a simple Excel spreadsheet that was occasionally updated when IT infrastructures were less complex. Not so today, as IT asset management has transformed and become more dynamic, especially as the workforce disperses, cloud services proliferate, and cybersecurity threats rise.
Today, ITAM is the end-to-end tracking and management of your company’s software and hardware with real-time visibility, and it’s core to your cybersecurity efforts because there’s no effective cybersecurity strategy unless all your IT assets can be comprehensively tracked, managed, and protected.
IT asset management ensures that organizations and their IT infrastructure remain agile and resilient in a constantly changing digital landscape, one where cybersecurity has never been more important. The combination of ITAM and cybersecurity strengthens vulnerability management, compliance efforts, and optimizes incident response, equipping businesses to face evolving cyberthreats.
Protect your valuable assets and cybersecurity investments
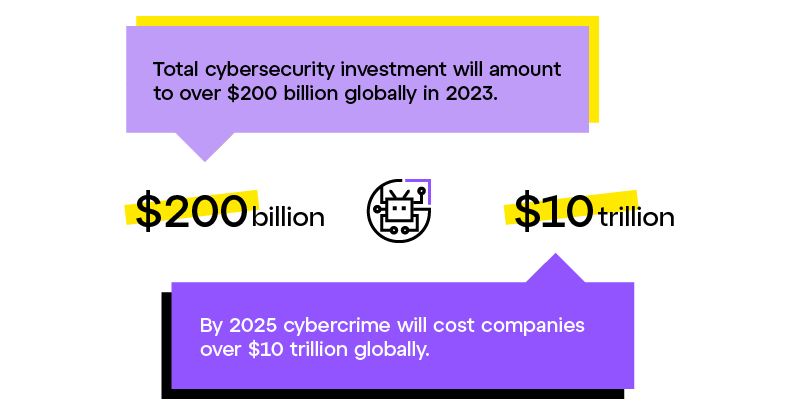
There's a lot at stake when it comes to protecting IT assets, and businesses invest a lot of money in protecting them from cyberthreats, typically about 10-12% of their overall IT budget. Total cybersecurity investment will amount to over $200 billion globally in 2023.
What’s driving today's massive expenditures in cybersecurity? First, security breaches are expensive. While it’s hard to estimate exactly how much money cybercrime costs global businesses, Cybersecurity Magazine has put the losses in the trillions of dollars, estimating that cybercrime will cost global companies over $10 trillion in 2025.
In addition, the digital workplace has become more complex with a larger surface area for potential attacks. Businesses are investing in cybersecurity efforts to manage:
- The persistent and evolving nature of cyberattacks
- The demands and vulnerabilities of hybrid work and distributed computing
- Increased data privacy and governance regulations
- The growing importance of IT to the success of the business
But investments in cybersecurity, by themselves, aren’t enough to protect your IT assets. You also need IT asset management to know what is happening across your entire network infrastructure. Without this visibility, and despite your cybersecurity investments, you may not be able to:
- Quickly detect threats, and collect detailed information on them, when they arise
- Investigate the precise source and nature of cyberthreats and their impact on your network
- Take fast and effective action to defend against those cyberthreats
What ITAM can do for your cybersecurity stance
ITAM gives you visibility into several key areas of cybersecurity, including:
- Patches and failed patches
- Vulnerabilities
- What’s new on your network
- What software is running on your network
- Any data leaks you should be aware of
You can see what devices are connecting with your system, how they’re connecting, how long they stay connected, what they do, and more. So, when cyberthreats happen and your system does get breached, ITAM provides you with relevant, timely data that you can use to investigate and mitigate the cyberthreat. For example, you could use ITAM to see whether any new software has been installed in your system over the last 30 days and which machines on your network said new software has been installed on.
Your ITAM can even notify you of unusual events or patterns, based on historical network data, that have been correlated with cyberthreats, enabling you to act quickly to avoid or mitigate attacks. ITAM enables monitoring who and what is on your network, whether internal or external users, what software they’re using (via software asset management or SAM), and what they’re doing.
4 benefits of integrating ITAM and cybersecurity
Real-time management with an IT asset management tool is an important part of a robust cybersecurity strategy. Here are 5 major benefits to combining the two.
1. Enhanced vulnerability management
Identifying vulnerabilities early is crucial for securing your IT environment. By merging ITAM's comprehensive asset records with vulnerability assessments, organizations gain enhanced visibility and proactive protection. This integration not only flags risks such as outdated software, end-of-life systems, misconfigurations, and unpatched security flaws but also aids in prioritizing and addressing these vulnerabilities efficiently. Furthermore, with a thorough understanding of the entire software landscape provided by ITAM, the process ensures that patch management is conducted without introducing new issues or destabilizing other system components, maintaining a robust and secure IT infrastructure.
2. Better compliance and ethical software use
Open-source software is available and free, which can be great in terms of saving budget, but can introduce challenges when it comes to compliance and support issues. Putting open-source components within your proprietary systems can cause more problems with compliance and support than you might expect.
Here, ITAM shines by offering you an all-encompassing view of software, including associated licenses and support levels/status. By shedding light on software usage patterns and licenses, ITAM helps businesses steer clear of expensive non-compliance penalties and uphold a high standard of ethical software usage. When you simply add open-source software and have no visibility into its impact on compliance and support, you’re potentially asking for unwanted surprises.
3. Improved management of the IT asset lifecycle
From the moment an IT asset is deployed to its eventual retirement, it travels through various phases. Managing this lifecycle, with the ability to track devices – and even wipe them when necessary using mobile device management (MDM) – ensures that every asset remains updated and secure throughout its existence.
If and when a security incident does occur, ITAM's extensive asset inventory can rapidly accelerate incident responses. Such timely interventions, such as wiping a lost/stolen device, can drastically reduce system downtimes, protecting both a company’s operations, its data privacy, and its bottom line.
4. Robust defense through better integration
A robust defense isn't just about having the best tools, but about ensuring they work seamlessly together. Integrating threat intelligence platforms like Bitdefender with ITAM systems lets businesses preemptively counter threats. Moreover, when combined with Security Information and Event Management (SIEM) solutions, which detect user behavior anomalies, continuous monitoring and prompt incident responses become the bedrock of a company’s cybersecurity approach.
It can also be beneficial to integrate ITAM with developer data protection solutions, such as Intel’s Software Guard Extensions (SGX) and AMD's Secure Encrypted Virtualization (SEV). While these tools provide a fortified security standard, they show their true potential when interwoven into a comprehensive IT Asset Management framework.
SGX integration
When SGX is integrated into ITAM you get Asset Differentiation. ITAM can identify and categorize assets equipped with SGX capabilities, enabling more nuanced security policies. For instance, data deemed highly sensitive can be flagged to only run on SGX-enabled hardware.
SEV integration
Incorporating SEV into ITAM provides enhanced Virtual Machine (VM) Security Posture. This enables:
Targeted Security Enhancement: By cataloging which VMs are on SEV-enabled hardware, ITAM enables organizations to specifically enhance the security of their most critical virtual environments. This targeted approach ensures that the most sensitive and vital workloads are given the highest level of security.
Strategic Resource Allocation: This integration is key for strategic decision-making regarding asset allocation. With ITAM's visibility into SEV capabilities, sensitive tasks can be deliberately assigned to the most secure hardware environments, optimizing both security and resource use.
Compliance and Proactive Management: Integrating SEV into ITAM aligns with compliance requirements for data security and enables proactive management of the IT landscape, ensuring that IT infrastructure keeps pace with evolving security technologies.
Get started with ITAM
By leveraging an ITAM solution to help shore up your cybersecurity posture, businesses can be better prepared to fend off threats proactively. As the digital frontier expands, and cyberthreats continue to evolve alongside it, organizations with an integrated ITAM and cybersecurity strategy are best positioned to tackle challenges head-on and capitalize on new opportunities.
LogMeIn Resolve helps your IT team track, monitor, and optimize your IT assets the easy way, in an all-in-one IT management and support solution that also includes integrated helpdesk ticketing, remote monitoring and management, remote support, and more at no extra cost.



